Last week WordPress.org closed 83 plugins from WPFactory. The closure caught their Algoritmika and WBW Plugins accounts too. Same parent company. There was a report on wp-content.co about a suspected backdoor in their premium EU/UK VAT for WooCommerce Pro plugin. A file called class-alg-wc-eu-vat-customer.php allegedly downloaded an external ZIP, modified WordPress directories, and transmitted data to a remote server.
WPFactory denied the file existed. WordPress.org closed the entire portfolio for review. WPFactory later acknowledged the file came from “a cached or outdated plugin package”.
I wanted to know for myself what the free versions actually contained. So I put these plugins through WP Beacon for a full audit. Here are my findings.
Building the haystack to search.
To audit at scale you need every version of every plugin. WordPress.org hosts plugin versions via SVN. There were projects that mirrored to git, but they’re outdated and didn’t preserve per-version commit history.
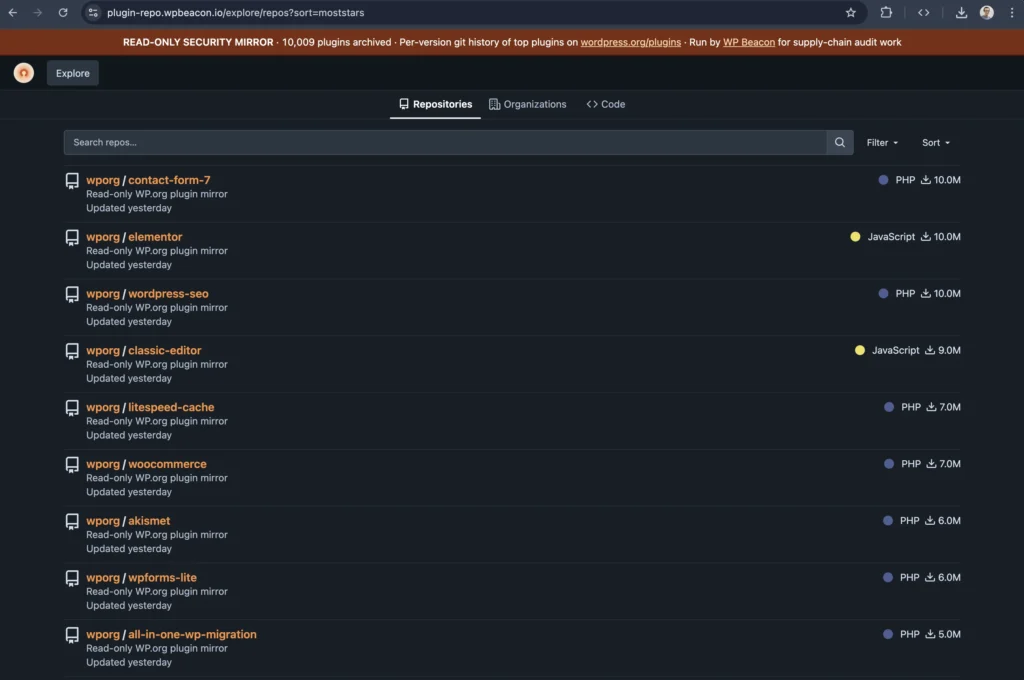
So I built my own this week. A 1.7TB box at InterServer running a self-hosted GitHub-like frontend at plugin-repo.wpbeacon.io with the top 10,000 wp.org plugins. Every version is tagged. After the WPFactory news I added the 83 closed plugins from across their family of accounts.
For attribution I crawled the SVN log into a per-revision database, then enriched each git repo so every release has a real committer name. wpcodefactory instead of a synthetic mirror identity.
That gave me pretty sizable haystack to dig through.
Auditing all 83 in parallel, then deeper.
I split the 83 plugins into batches and spawned Claude Code agents in parallel. Each agent cloned its assigned repos, ran a 14-pattern IOC sweep across full git history, looked for the article’s named file, and checked for known WPFactory non-malware patterns.
Each agent finished in roughly 10 minutes. A 14-pattern regex sweep finds the obvious. It does not catch obfuscation. Rename a function, split a URL across an array, build a string at runtime, and the regex finds nothing.
So I ran a second pass. This round read every PHP file in every plugin’s HEAD release line by line. Looking specifically for third-party uploaders, hidden persistence, update-channel hijacking, auth backdoors, phone-home plus RCE pairings, and disguise techniques.
Still no malware.
Total: 83 plugins audited
CLEAN: 32
GUIDELINE: 51
SUSPICIOUS: 0
MALICIOUS: 0The mentioned backdoor file does not exist in the free versions.
The named file class-alg-wc-eu-vat-customer.php has never appeared in any version of any of the 83 free plugins. Git history goes back 11 years on the oldest one. No version of eu-vat-for-woocommerce (the free companion to the paid plugin) has ever shipped that file.
What does exist is a sibling. class-alg-wc-eu-vat-customer-meta-field.php. It’s an admin profile field implementation. No HTTP calls. No file writes. No exec primitives. It’s not the same code.
WPFactory’s claim is true for the free package. That doesn’t make them innocent.
I suspect the real reason for the closure is guideline violation, given the history.
Of the 83 plugins, 51 bundle one or both of these vendor libraries.
vendor/wpfactory/wpfactory-cross-selling/vendor/wpfactory/wpfactory-promoting-notice/
Both are admin-promo banner libraries that phone home to wpfactory.com to fetch banner content. The cross-selling library hits a JSON endpoint at wpfactory.com/wp-json/advanced-ads/v1/groups. Promoting-notice does the same with different endpoints. The banner content is rendered in the WordPress admin UI on the user’s site.
WordPress.org’s plugin guidelines don’t allow this. Phone-home behavior requires informed user consent. The library loads automatically on every plugin install. There is no opt-in. There is no toggle. The user gets promo content from WPFactory whether they want it or not.
This is what I suspect is the actual reason WordPress.org closed the portfolio. Not malware.
What this looks like in the audits.
Each free WPFactory plugin’s GitHub-style mirror is at plugin-repo.wpbeacon.io/wporg/<slug>. You can browse the actual code, see the committer history, click through the diffs. The library is not subtle. It’s literally named wpfactory-cross-selling. It loads admin notices that promote other WPFactory products.
This isn’t a backdoor in the free versions. The article’s named file is paid-only. WPFactory was correct about that and probably winning on the technicality.
A temporary closure is a chance to recover.
The cross-selling and promoting-notice libraries phone home for vendor promo content with no opt-in. They auto-load on every install. wp.org’s guidelines on phone-home behavior aren’t ambiguous. They aren’t new. If WPFactory wants to resume activity on wp.org, I recommend they do the basics and follow the guidelines.
Other vendors caught doing similar things this year cleaned it up. Greenshift removed the offending code. WP Product Feed Manager lifted the paid product cap and stripped its Go Premium upsells. WPFactory has been bundling these libraries across dozens of plugins for years.
Where does that leave us?
If you run any of these 83 plugins from WordPress.org, you’re not compromised. The library is annoying but not malicious. As of today the plugins are still marked “closed pending review”. Once the WordPress.org plugin team and WPFactory work out the issues, the plugins will likely be restored. That remains to be seen.
What is knowable is what’s in the raw data in the WordPress.org plugin repo. And now, the audit data is viewable at plugin-repo.wpbeacon.io. Every commit, every committer, every release. Searchable, browsable, real. Feel free to dig in yourself.

